As more and more organizations and governmental institutions are getting digitalized the threat of the cyber security breaches is immense. The result of this is obvious - the need for experts in this work area grows significantly day by day and more people choose cyber security careers as their path in life.
In short, cyber security is exactly what it sounds like. It is the practice of protecting sensitive data from hackers, thieves, and other people who are interested in illegal actions. Cyberattacks are an evolving threat to everyone, from the organizations' chief managers to their employees and customers.
The long term for cyber security would be the practice of defending digital devices like computers, mobile devices, networks, servers, systems, and data from malicious attacks. The synonym of the cyber security would be informational technologies security.
A strong cyber security system must consist of multiple layers of protection that are spread throughout the whole computer network. But that is not the only important thing in this work area. To operate to the maximum safety, informational technologies security requires people that are capable of making the right choices to secure the data. The good news is that everyone can aim for cyber security careers and learn how to recognize and avoid cyber security threats.
Table of Contents
Why It Is Cyber security So Important?

Latest Deal Active Right Now:
EXCLUSIVE 25% OFF
On DataCamp Subscriptions
Follow the Datacamp promo code link & get an exclusive 25% OFF Datacamp subscriptions. Act now while the offer is still available!
A quote from Josh Feinblum, the CSO of DigitalOcean organization says: “We live in a world of unprecedented connectedness”. Every year, there are more and more devices that are connected to the internet. With each of those devices, we submit more data about ourselves, our daily lives, and our activity. Although with all these actions we are trying to improve the quality of life, it also exposes us to more risks than ever before.
The personal data is spread through so many places in the network, it might seem overwhelming trying to control it. Gartner, the world’s leading research and advisory company, states in its’ report that worldwide information security costs around 124 billion dollars. This includes cloud, data, identity access, application, and many more security services.
Cyberattacks have the potential to cripple many business companies, and most of them recognize the importance of their network safety. Cyber security careers have been enhanced over the past years. The statistic that leads to the growth of jobs in informational technology security is undeniable: over six million data records are stolen or lost worldwide every single day.
Other than business companies, there are many more institutions that can be harmed harshly by cyberattacks. Governmental institutions, politics, diplomats and social wellness of the society can be affected even more. Scandals like Cambridge Analytica happen with the help of cyber security breaches and in result, they influence nations’ elections, divide the people and lead to the rise of propaganda.
With all these factors it is clear that cyber security became one of the most important security measures in the modern-day world. The question is, what do you need to get started?
Before Getting Started
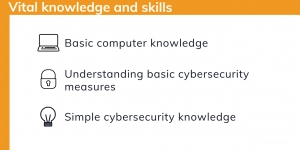
For those who are considering taking on the path of cyber security careers, it is important to evaluate some of the current skills. Although there are no crucial requirements to begin learning about the possibilities in the cybersecurity, some are still vital to do so:
- Basic computer knowledge. The whole informational technology security thing mainly revolves around the computer. If you don’t know how to operate it successfully, it will be extremely challenging learning about cyber security and how it works. On the other hand, if you are interested in jobs in cyber security, means you should already have a decent understanding of how computers work and their peculiarities.
- Understanding basic cyber security measures. Although this may seem like an overkill before starting the digital security courses or training but having a basic understanding of how cyber security measures work can make the learning process a lot easier.
- Simple cyber security knowledge. Same as already mentioned above, it might be helpful to do some additional research about your future career and its’ peculiarities. Get to know about simple informational technology security terms like a virus, Trojan, phishing, ransomware, etc. This kind of knowledge will be useful to understand the purpose of cyber security careers and jobs.
While these are only simple steps that will help you along the to become an expert in this work area, there is one that will help you the most. It is motivation and eagerness to learn. Cyber security is a complex field to master but it’s not rocket science. If you are willing to put in the hours in learning and working hard, you’re halfway there.
Getting Started
When starting to pursue a career in cyber security it is important to understand that this field is similar to engineering or even healthcare. There are many branches of the work area that you can work on, and each of them requires a different skillset.
Following the story of Akshay Sharma, a computer science expert, after working as a developer for years he decided to start working in the cyber security area. Prior to his experience, he thought that it would take no time to become an expert in this field. To his disappointment, it wasn’t so easy. Cyber security careers most of the time are a new, clean-slate experience, even for the advanced IT experts.
Recommendations
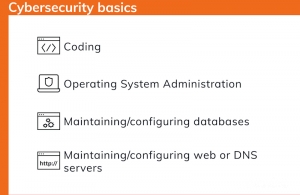
Everyone needs time to adapt, so give yourself time and don’t worry about the path you’ll take at first. To get started, these are the recommendations to get a good overview of cyber security basics:
- Coding. Getting some basic coding knowledge can help to see a different point of view of web pages and applications creation. Knowing how they are made, it is easier to determine what is causing the problem. Programming languages like Python, HTML, and Javascript are beginner-friendly so it’s best to start with them. Having trouble to find where to learn it? Head over to BitDegree courses and type in the needed one. You will find your answers in no time.
- Operating systems. The most common computer systems in cyber security are Linux and Windows. If you have the possibility, start by using the Linux one and learn how to administer it using the Command Line Interface. This skill will be extremely useful no matter what path you are going to choose in informational technology security. CLI is opposed to the Graphical User Interface (GUI).
- Applications. Pursuing cyber security careers requires the skill to maintain, configure, and run common computer applications such as a database, web server, or DNS server.
Don’t give yourself a harsh time by trying to learn everything at once. Start by learning the basics and try to grow your skills over time. Continuous research, learning from your mistakes and having a critical mind will be the key parts of your entire career.
Working in Cyber security
Jobs in cyber security are versatile and welcome people from both, technical and non-technical backgrounds. When you think first about a job as an information technology expert, your first thought is that you need to be professional in computer science. That is not entirely true. Having a non-technical background in cyber security is not a disadvantage but an opportunity. Let’s take some time to separate the paths of cyber security careers:
Technical Background Possibilities:
Having experience in development, programming, and computer science is surely a benefit. It enables the person to decode certain computer-related issues at a faster pace. All these skills are easily transferable to a cyber security role. Programming experience helps a lot when it comes to detecting malicious code and how to defend it. Web developing knowledge turns out useful when it comes to cross-site scripting. Software engineers can do a greatjob mitigating vulnerabilities such as buffer overflows. Some of the jobs that can be acquired in cyber security with a technical background are:
- Virus technician. This job requires knowledge about the latest viruses on the ‘market’. A virus technician is a person that develops software to fight off the viruses and protect the network.
- Security engineer. The person that works as a security engineer monitors the network for security breaches, looks for vulnerabilities that can be abused by hackers, and develops security plans.
- Cryptographer. The main goal of a cryptographer is to create encryption algorithms to secure data. The reason for this is simple - if the hacker steals the data, he won’t be able to open it and abuse it. Additionally, cryptographers also analyze and decipher the algorithms.
- Penetration tester. This is quite the opposite of the other cyber security careers. To put it simply - it is a hacker that is hired by an organization to test its’ defensive systems. Penetration testers follow ethical rules that are agreed with the client company and look for possible breaches that could be found in their systems.
- Easy to use with a learn-by-doing approach
- Offers quality content
- Gamified in-browser coding experience
- Free certificates of completion
- Focused on data science skills
- Flexible learning timetable

- High-quality courses
- Nanodegree programs
- Student Career services
- Nanodegree programs
- Suitable for enterprises
- Paid certificates of completion
- A wide range of learning programs
- University-level courses
- Easy to navigate
- University-level courses
- Suitable for enterprises
- Verified certificates of completion
Non-technical Background Possibilities:
While having experience is considered an advantage, it is not the only way to work in cyber security. Having a non-technical background does not always put you at a disadvantage. Coding and development are not the only activities in this field of work. Some positions can be obtained with whatever skills that you have. For example:
- Technical writer. If you’re an avid writer that has a good grasp for grammar, you might find yourself writing technical articles for cyber security companies. These articles aim to spread the information, guides, and tutorials on how to achieve certain goals or learn something related to the information technology security field.
- Network administrator. The goal of this job is to secure the network and provide access only to the people that have the permission to do so. The network administrator monitors the activity and ins and outs of the network. The experience that comes from this position comes in useful when seeking higher cyber security careers.
- Security operations center analyst. This person, within a team, works 24/7 and reports every incident that threatens the safety of the government. A SOC analyst reports vulnerability analysis and offers recommendations that deny possible cyberattacks.
- Vulnerability analyst. Similarly, as SOC analyst, vulnerability analysts’ goal is to find critical flaws in the network, system or applications. This specialty requires the use of certain tools that come in the clutch while looking for safety bugs. It is important to stay on top of the latest threats and actions on how to prevent them.
- Cyber policy analyst. A strategic person that develops procedures and requirements for the governmental or public companies to assure cyber security. A cyber policy analyst assists organizations to implement cyber security policies to their structure.
As you can see the field of cyber security offers a lot of possibilities to people with or without a technical background. Every position is possible to achieve if there is a will to strive forward.
Cyber security Training

For those who are wondering how to begin pursuing cyber security careers and have no clue where to start training, BitDegree offers a solution. In the courses section of our website, you can find a dozen lectures that will guide you on the path of cyber security. Take a look at the staff picks:
- Cyber Security Training: From Zero to Hero. The course by Gautam Kumawat, who is an expert in the field of cyber security, is a great way to easily gain practice. In Cyber Security Training, you will find ethical hacking and penetration testing knowledge. The course does not require much to start - only basic internet surfing experience and motivation to learn.
- Networking Basics: The Complete Guide. This course is presented by Abishek Sagar. This networking course covers everything you need to build and protect networks. Be sure to keep the motivation high as the course progresses, because the footage lasts more than 4 hours and has 33 lessons.
By the way, if you have any financial struggles, we don't want that to stop you from learning. Apply for cyber security scholarships for online classes and your course fees might be funded for you.

Did you know?
Have you ever wondered which online learning platforms are the best for your career?
Conclusion
The field of information technology security is still growing and offers many possibilities for those who are willing to put in the hours to achieve cyber security careers. The need for experts is at an all-time high because of the unprecedented connectedness. Follow the tips and start your journey on fighting cybercriminals now.